Inside SJAC’s Open-Source Investigative Team
Over the past ten years, SJAC has used its open-source database software ‘Bayanat’ to compile nearly two million videos, interviews, and documents related to the Syrian conflict. All of this evidence undergoes a systematic labeling process to reveal connections between different documentation from different sources. While SJAC continues to collect and process new documentation and answer data requests from legal authorities, SJAC’s newly established Open-Source Intelligence (OSINT) team proactively utilizes existing documentation to investigate serious crimes and draft reports for policymakers and the public.
Thus far, SJAC’s investigators have completed four publicly available investigations, which present evidence of “Double Tap Strikes” on civilians, Syrian government snipers targeting civilians at “Crossing Points,” modified double tap strikes on hospitals, and Syrian government forces burning the bodies of individuals killed in summary executions.
In this article, SJAC is sharing a behind the scenes look at how its investigators sift through millions of pieces of data to compile evidence of crimes.
What does SJAC investigate?
The core of SJAC’s Bayanat database is open-source information from platforms like Youtube, Twitter, Facebook, Telegram, and Syrian news sites that collate user generated content. Because much of the information SJAC collects depicts graphic content, our Data Analysis Team proactively scrapes and preserves videos and images from social media sites prior to removal by content moderators. For the past ten years, SJAC’s data analyst have shifted through terabytes worth of data, labeling documentation and creating an easily searchable database of thousands of crimes.
SJAC’s Investigators are responsible for finding the patterns within this data, to draw out the most serious, systematic crimes. SJAC’s team of investigators are all Syrian and many have been working in SJAC’s database for many years, experience they draw on when identifying new leads.
For SJAC’s report “No Escape,” the lead investigator had previously logged instances where Syrians were targeted by government snipers while crossing through chokepoints. He suspected that these types of attacks, at crossing points between government and opposition held territory, represented a broader pattern of crimes. First, he performed a series of searches within Bayanat, to collect all potentially relevant data already gathered by SJAC. He initially found eight incidents that matched the criteria, later narrowing it down to three incidents that seemed to match the patterns under investigation. The five incidents that were not included in the report either lacked sufficient information or, in the case of one incident, was found to be fake.
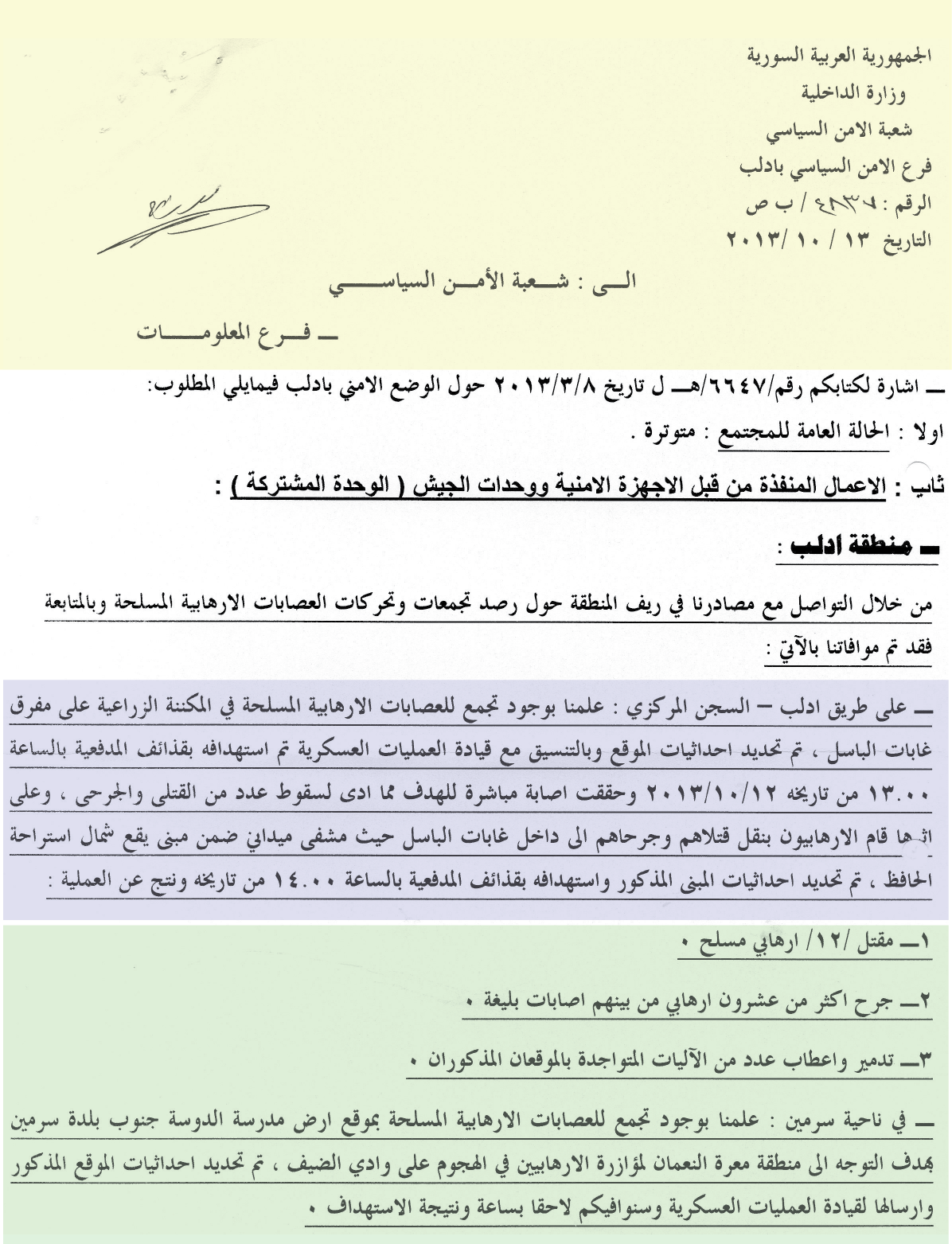
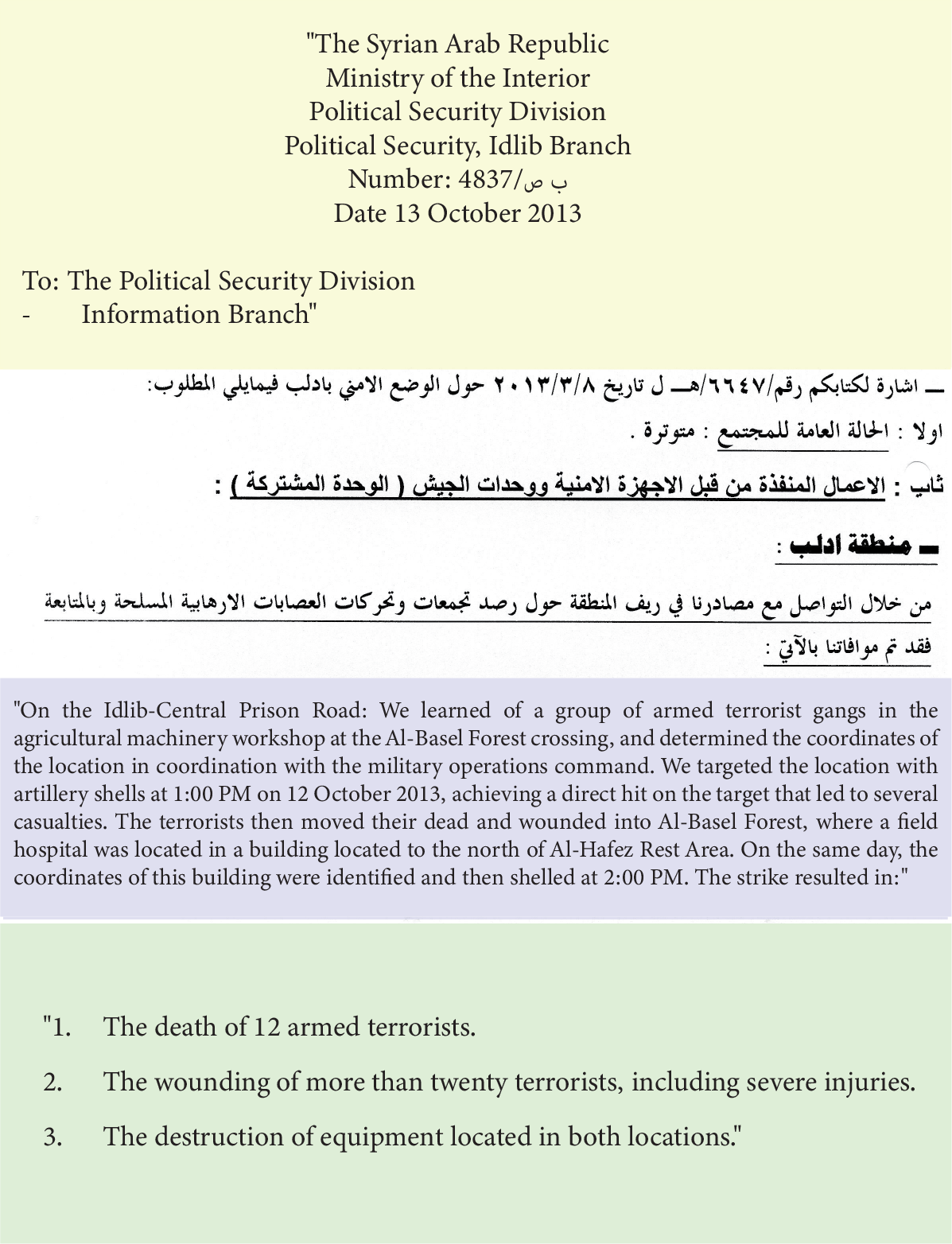
Next, the investigator worked to collect additional sources of evidence to provide corroboration. SJAC’s analysts perform additional, targeted open-source searches and search SJAC’s offline database for field documentation, including witness interviews and government or ISIS documents. The investigators will also reach out to SJAC’s documentation team on the ground to request any additional interviews pertaining to the topic under investigation. In the case of ‘No Escape,’ SJAC’s team was able to identify an internal document from the Syrian Ministry of Defense acknowledging incidents of snipers targeting civilians.
Ensuring Credibility
Next, SJAC’s investigators use a variety of techniques to bring all of this evidence together and ensure credibility. First, they assess the credibility of the initial, open-source evidence collected. For example, when reviewing videos of a purported incident on Youtube, SJAC’s investigator will gauge the authenticity of a video by checking who published the video, when it was published, and if the other videos on the channel seem authentic. Videos posted by local media outlets, eyewitnesses, and survivors are highly credible so information from them is scored higher and might be used to confirm information posted online by an anonymous account with no other content. However, SJAC considers all data it finds, and even unauthenticated sources may be used after stringent review.
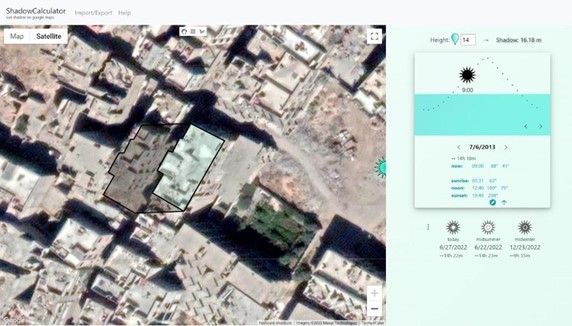
Investigators can then analyze whether the videos corroborate documentation from other sources. One way to do this is to ensure that the video was posted after the alleged incident and that it was filmed at the correct time of day. Videos and other evidence can be run through reverse image searches to check the primary source and original posting data. SJAC’s investigators use InVID’s Chrome extension that tracks the source of an image, the date it was created, and if it was manipulated, however, TinEye, and Google Image Search are also viable tools. SJAC’s investigators further use shadow and sunlight analysis software to check the time of day an image or video was taken and confirm the timeline matches that of eyewitnesses or local news reports.
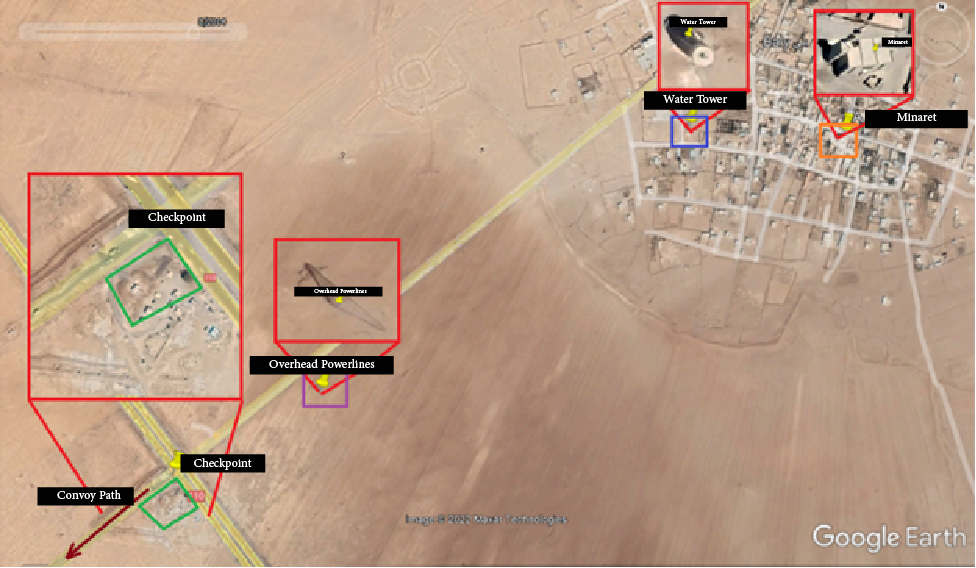
Investigators can also corroborate the location of alleged incidents. As part of research done for SJAC’s report “No Escape,” investigators discovered an article from a defector that described an area where government snipers targeted civilians moving between government and opposition territory. To verify this report, SJAC looked for supporting video and found a clip that claimed to be from the Karaj Al-Hajiz neighborhood in Aleppo where the incident reportedly took place. In the video, the dome of a nearby mosque is visible, and along with other surrounding structures, helped investigators confirm the precise location of the incident.

The Future of Data Analysis
The dangers of documenting crimes on the ground combined with sophisticated misinformation campaigns continue to be roadblocks to accurately documenting the Syrian conflict. However, our OSNIT investigative team is creatively working around these challenges, using ten years worth of documentation and an array of investigative tools to ensure that over a decade into the conflict, SJAC is still able to shine a new light on violations and advocate for justice.
_________________________
For more information or to provide feedback, please contact SJAC at [email protected] and follow us on Facebook and Twitter. Subscribe to SJAC’s newsletter for updates on our work.